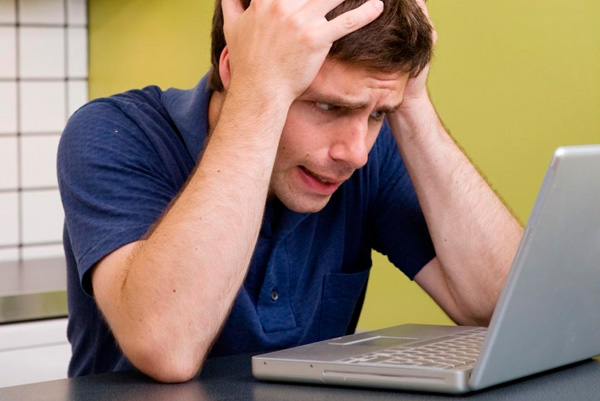
Can you imagine this worst case scenario? Your password manager just got hacked. That is the trouble with a strategy, let me put all of my eggs in one basket. On the other side, what other real options do we have? They say, do not use the same password for all of your various devices.
OK, we got it, but who is going to remember dozen of different passwords. Now, you see what is the big problem here. When it comes to the password managers, we expect from them to be bulletproof in terms of flawless cyber security. When they fail, what are we supposed to do?
Passwords are going to be our most annoying problem for quite some time. We are literally helpless. Every now and then, you hear about the more or less successful innovations in this field. There are some experts, who are suggesting us to use Emoji symbols as a password alternative.
Can you believe it? How about body implants? Can this work for you? Do we really need to trade our privacy for an adequate password? The more we talk about passwords, the more frustrated we eventually become. Should we use the word password for our only password?