Sooner or later, this way or another, you are going to be ad-stabbed-back by all those shiny, friendly and colorful service providers. This has already happened with Google, and the history repeats itself with Mozilla. We have to admit, we are a little bit heartbroken. All great ideas have greedy endings.
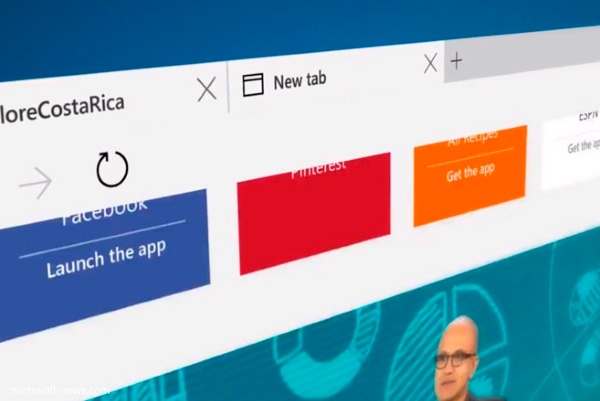
Mozilla is about to introduce the thing called Suggested Tiles. So, what is the big deal about it? Well, this is a new kind of advertisement. You are going to search, and Mozilla is going to suggest. If you do not like it, you do not have to use it. As simple as that. When you put it this way, it sounds like a fair deal.
However, there is a catch. Mozilla’s suggestions are actually based on your browsing history. Now, it does not sound so fair, does it? We do not care about the things you advertise. Nevertheless, we have a right to ask, how did you create your offer? Based on what data?
Somehow, we have a feeling that this particular corporate greed is going to hit back Mozilla like a boomerang. Mozilla’s power is directly derived, or even better to say, borrowed from us, the users. No users. No trade. You have to maintain a careful balance. Otherwise, we will have to migrate to some other ad-free place.